Онлайн кассовый аппарат - это электронное устройство, которое используется для регистрации и учета продаж
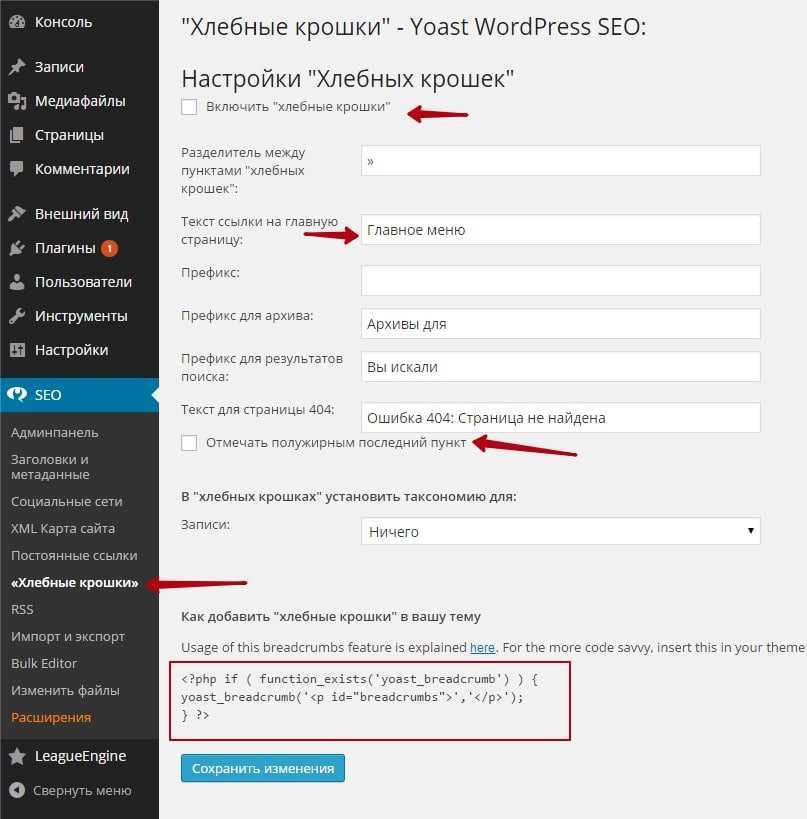
Как сделать хлебные крошки для сайтов и блогов в Wordpress. Есть несколько способов, давайте
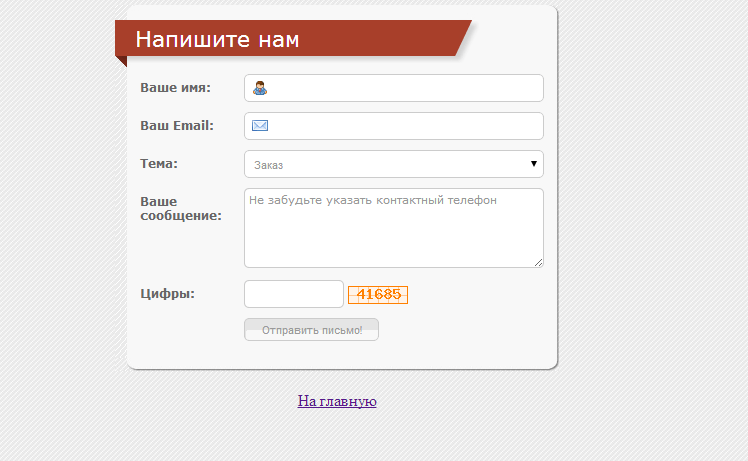
Форма для добавления посетителем статьи на сайт, без регистрации. Frontend Posting - позволяют посетителю/пользователю
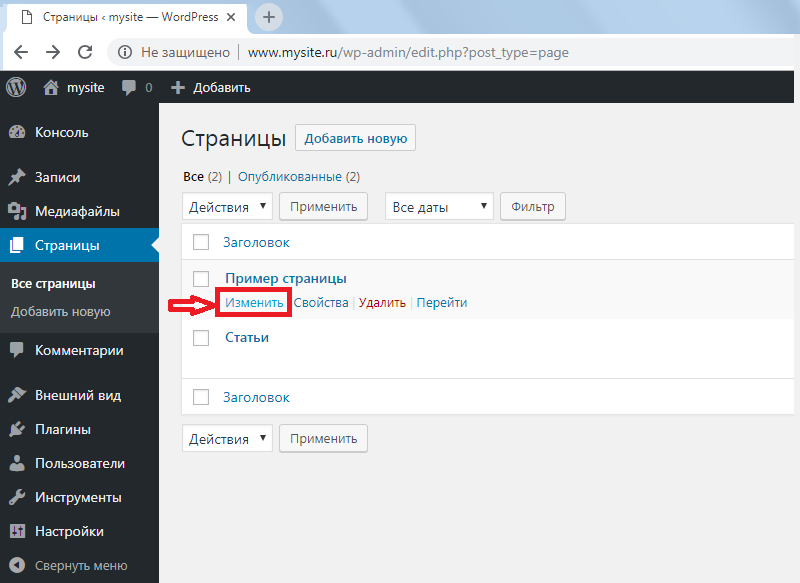
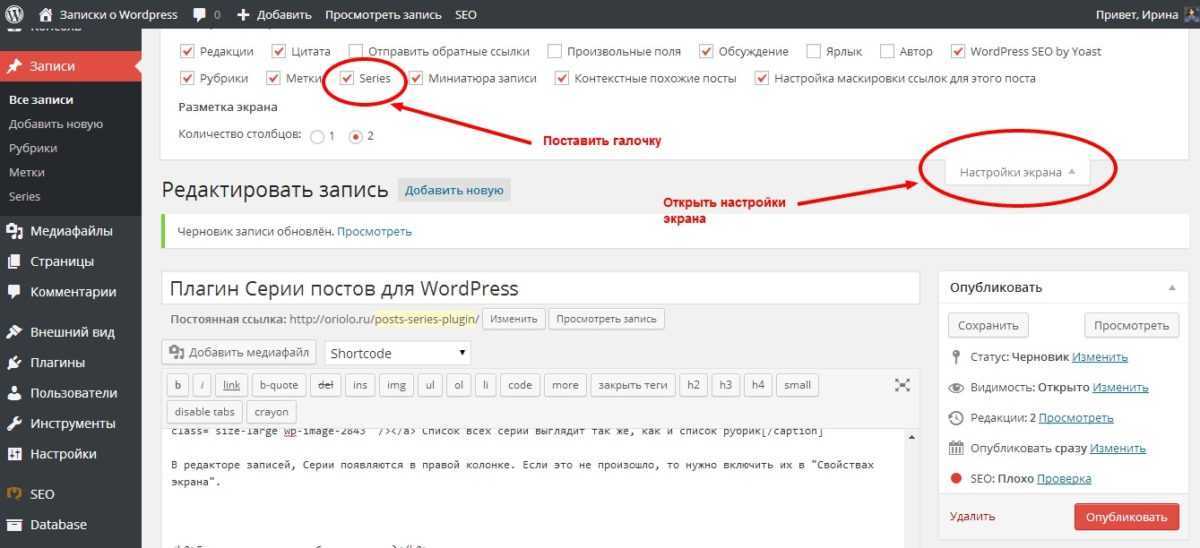
Сегодня мы доберемся до этого главного и я покажу, как публиковать статьи и делать
Display related posts without slowing down your website! Link all your existing content with
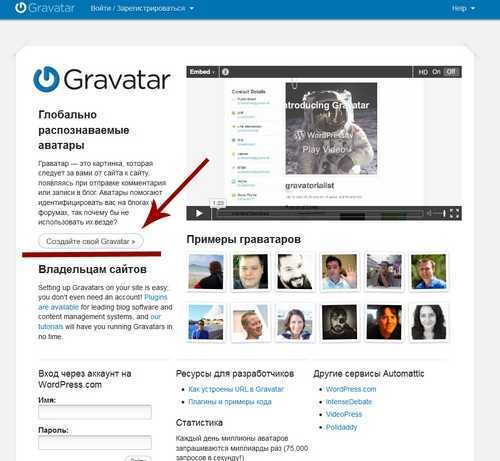
Из статьи вы подробно узнаете как создать аватар в WordPress. Подробное руководство по gravatar
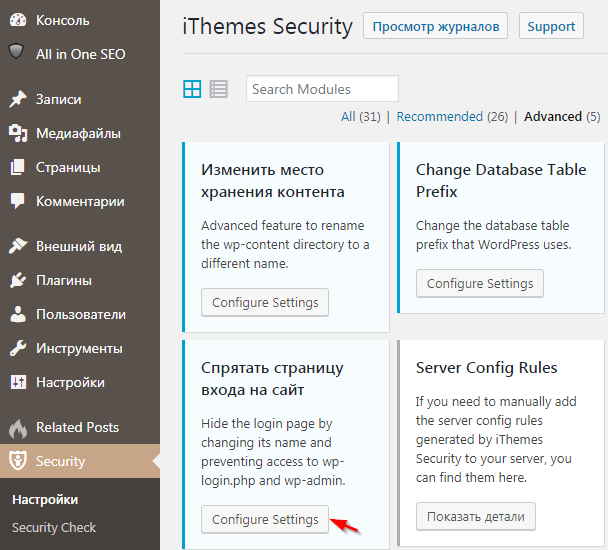
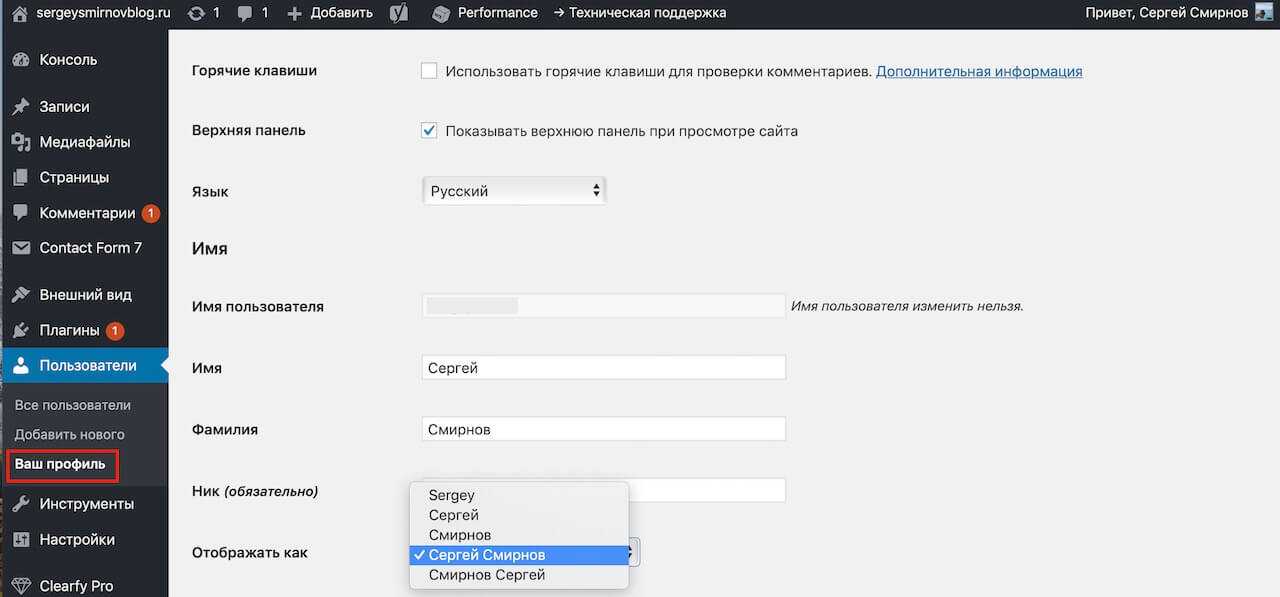
Админка Wordpress: вход, настройка и защита от взлома. Как зайти в административную панель Вордпресс.
В этой статье разберём, как подключить на сайт простой адаптивный слайдер ItcSlider. Рассмотрим его
В этой статье рассматриваются 5 лучших плагинов RSS-рассылок для WordPress
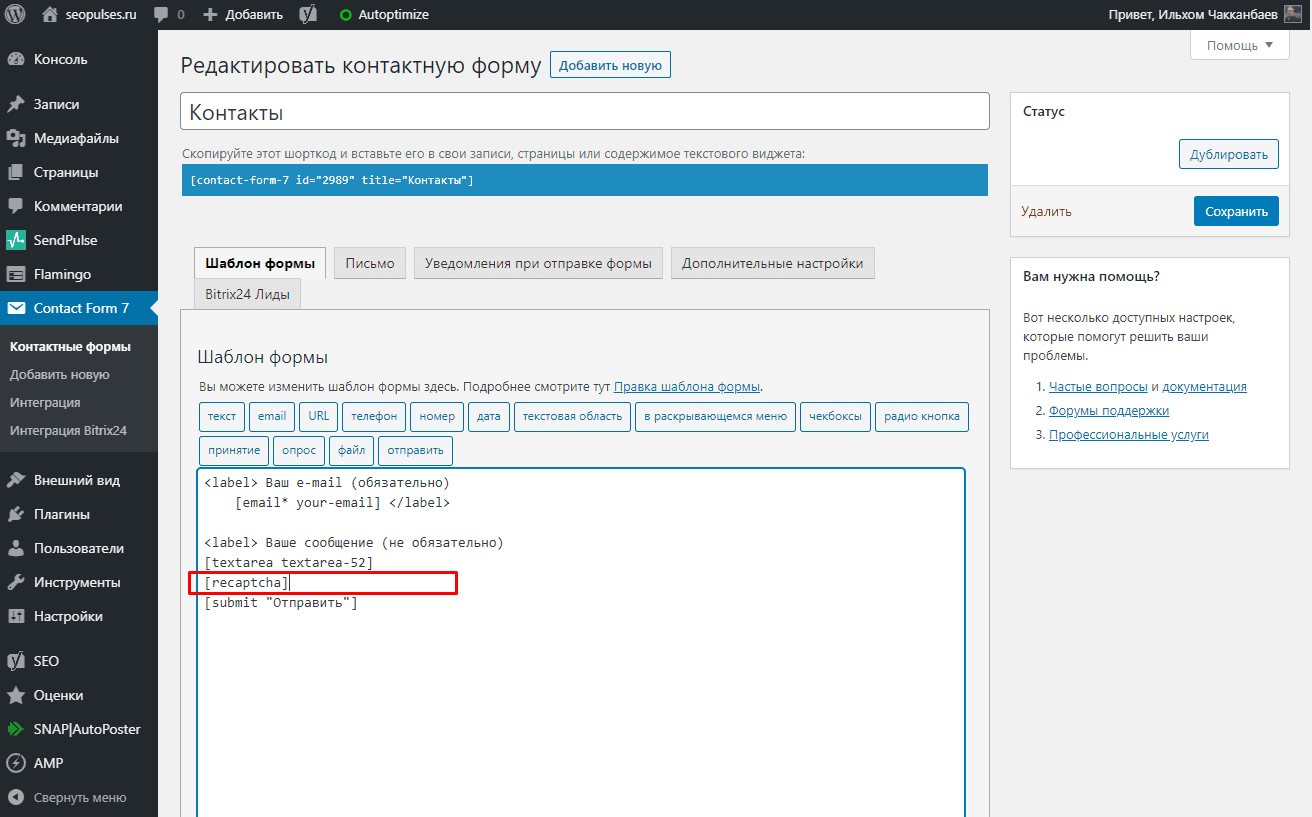
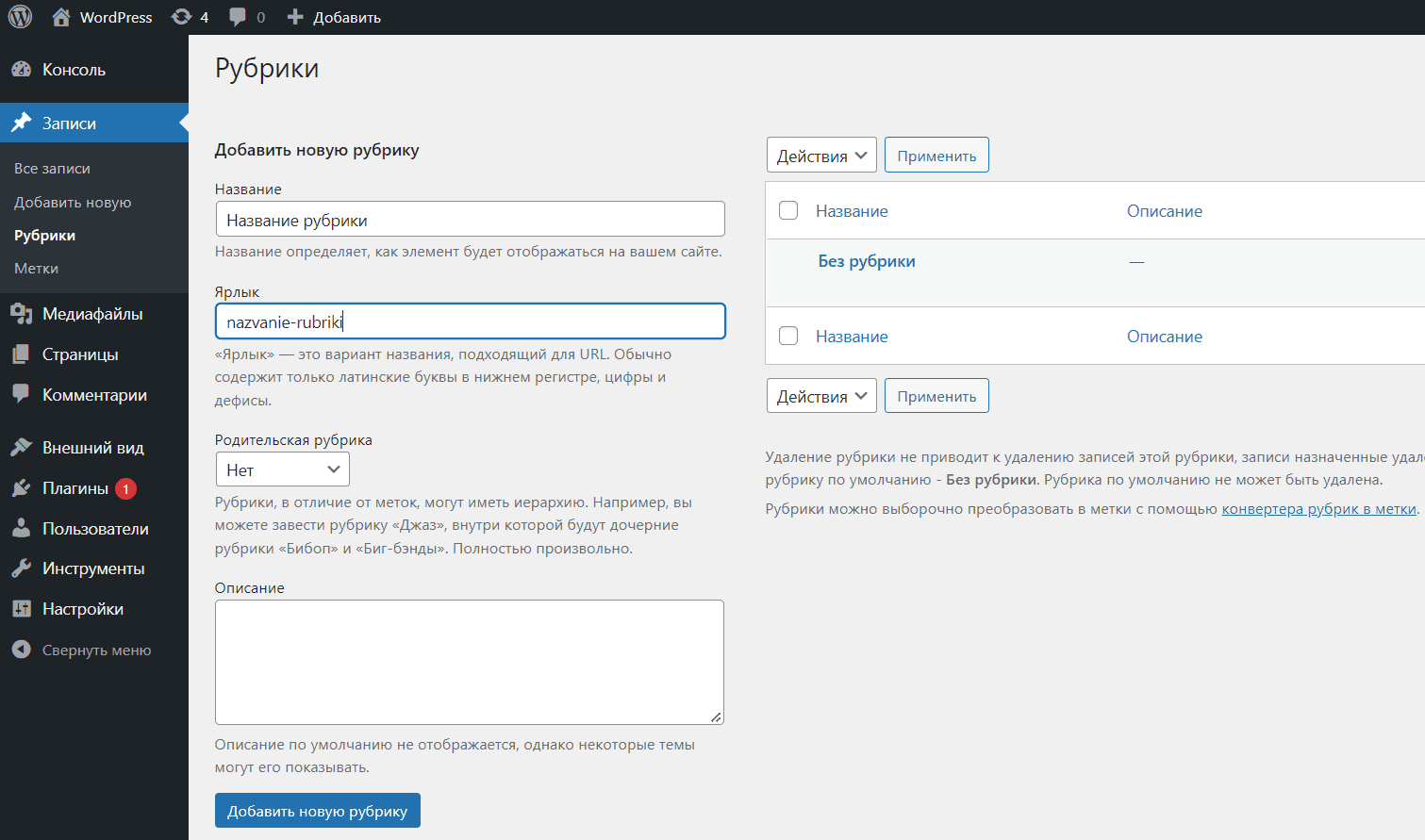
В сегодняшнем практическом уроке мы рассмотрим основные шаги, которые вам нужно сделать, чтобы добавить
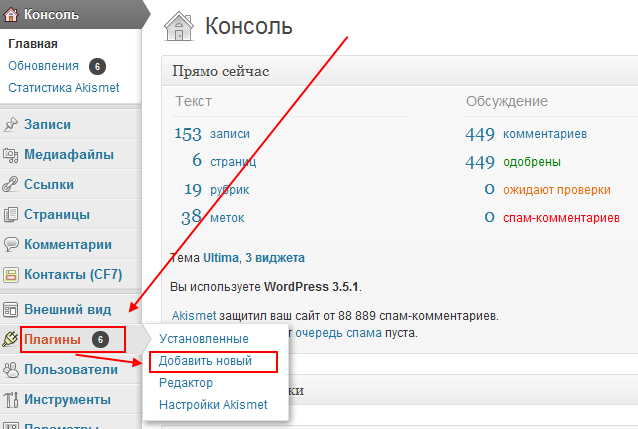
4 способа как установить плагин в WordPress: через интерфейс админки (из каталога и вручную),
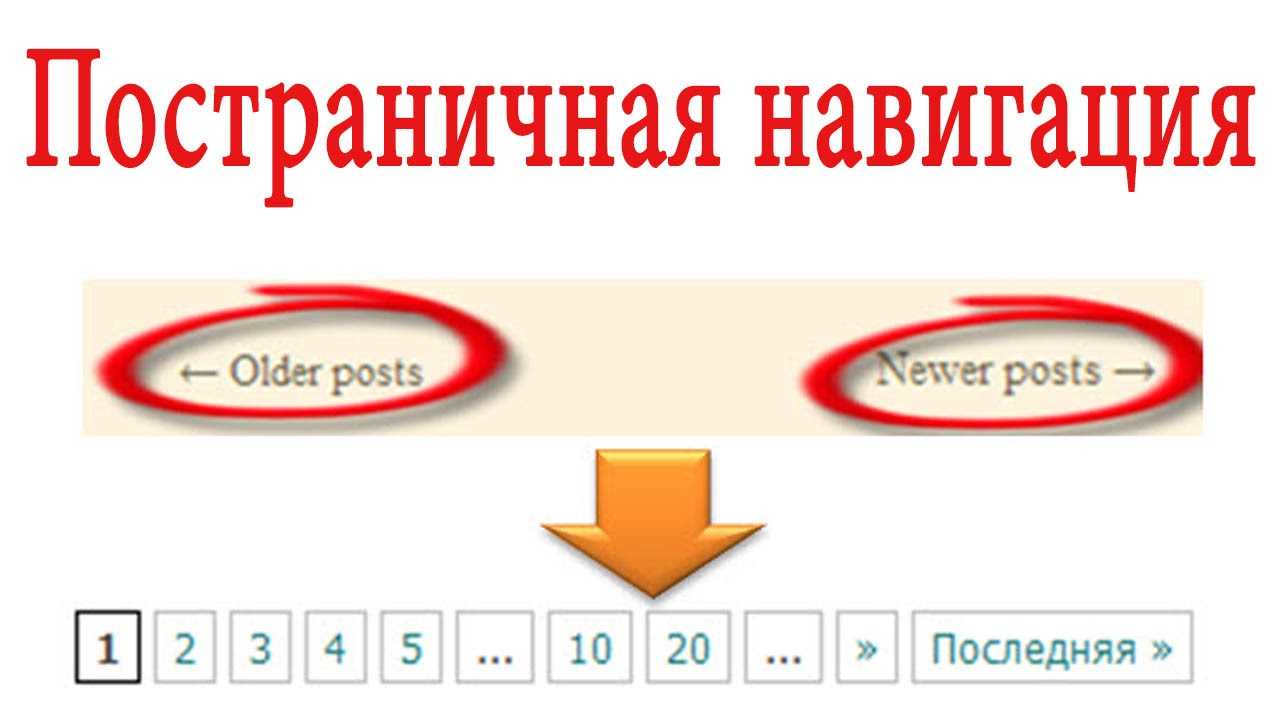
Как сделать постраничную навигацию комментариев на блоге с помощью кода
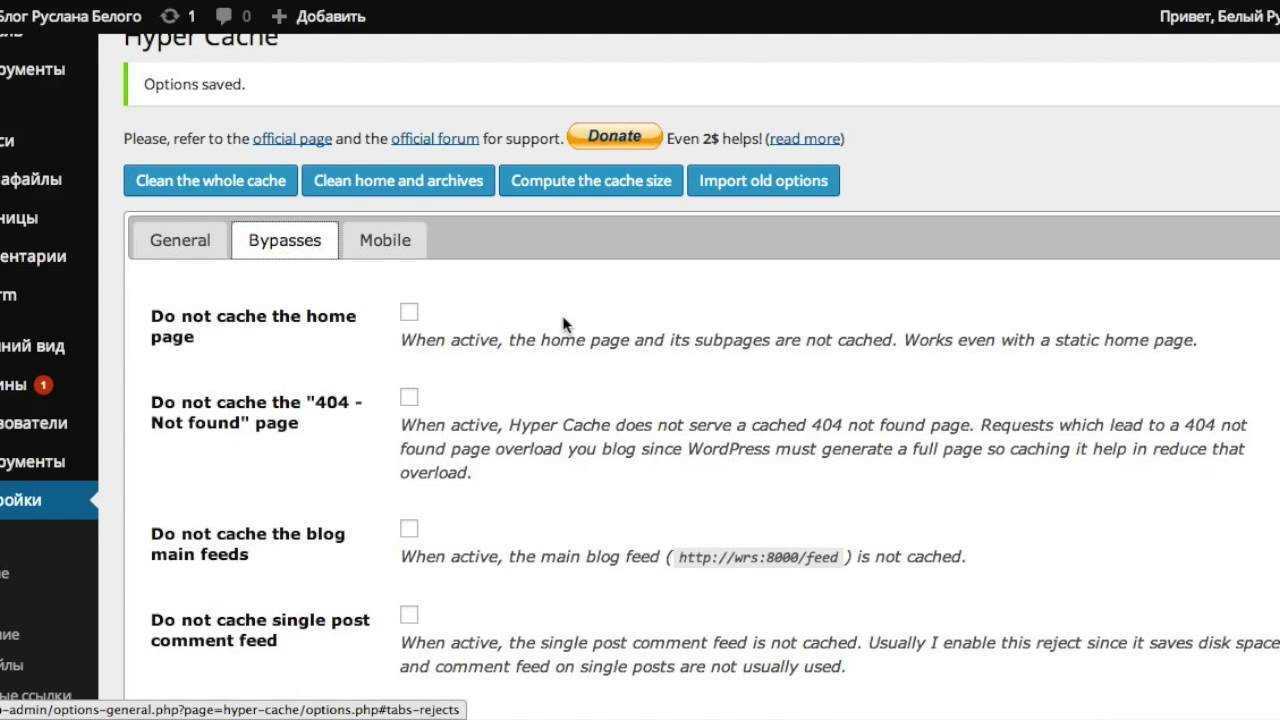
Для высокого ранжирования сайта со стороны поисковых системам важна скорость загрузки страниц сайта. Чем быстрее
Плагин Breadcrumb NavXT позволяет добавить в WordPress хлебные крошки, которые служат для улучшения навигации
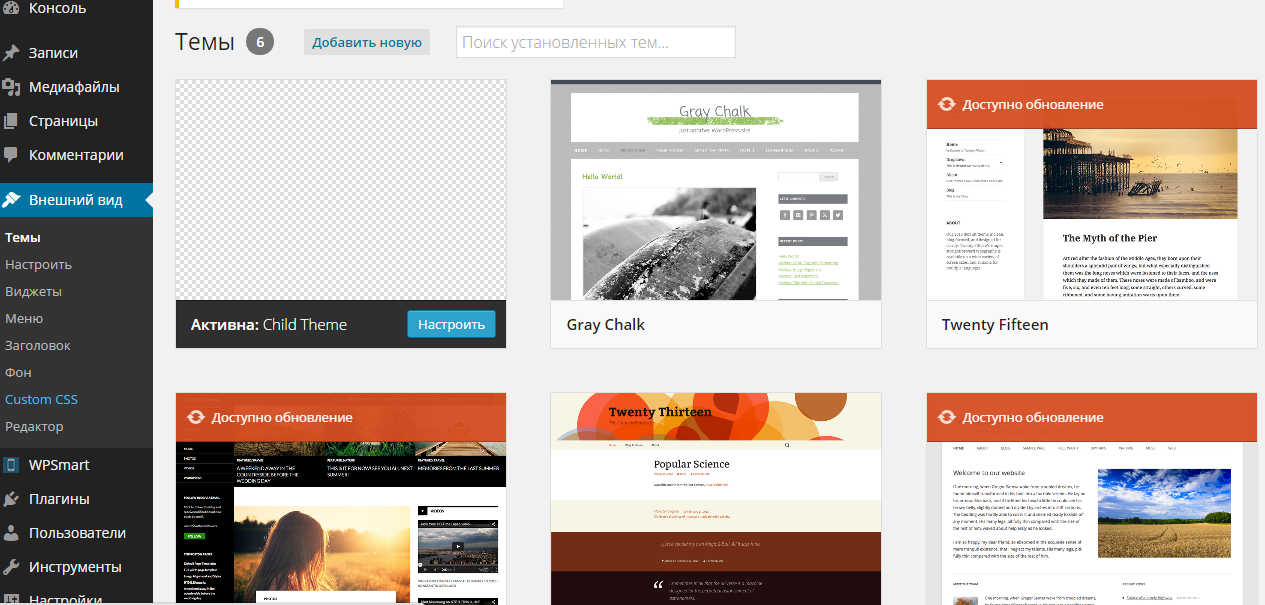
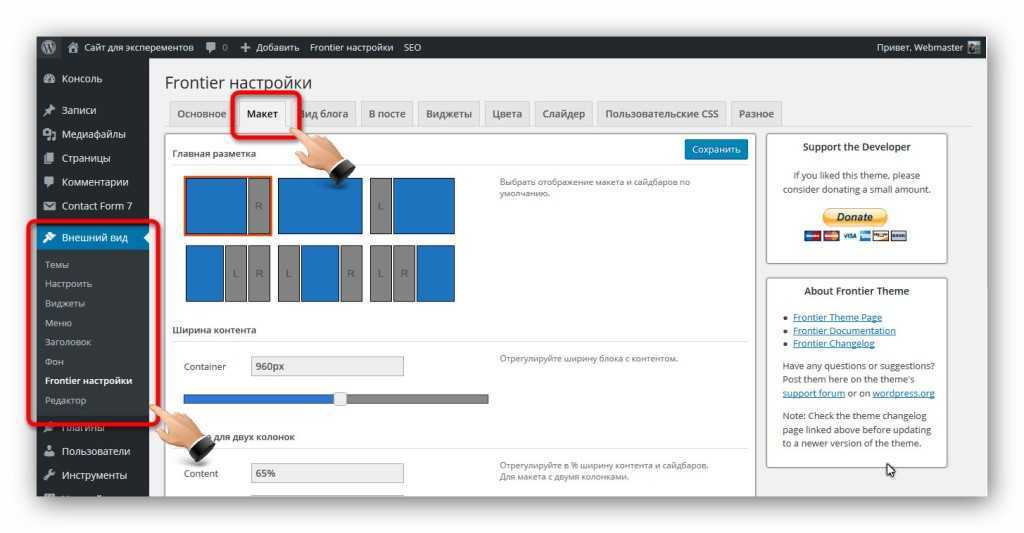
База знаний о хостинге и серверных технологиях Timeweb Community: Как выбрать шаблон для WordPress.
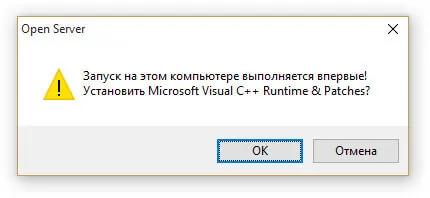
Что такое Openserver. Начало работы или как установить WordPress на Openserver. Как создать базу
Очень важно выполнить настройку ЧПУ в WordPress до начала публикации. Настройка ЧПУ положительно влияет
Как узнать id категории в WordPress! ID поста в WordPress! id меток (теги), страниц,
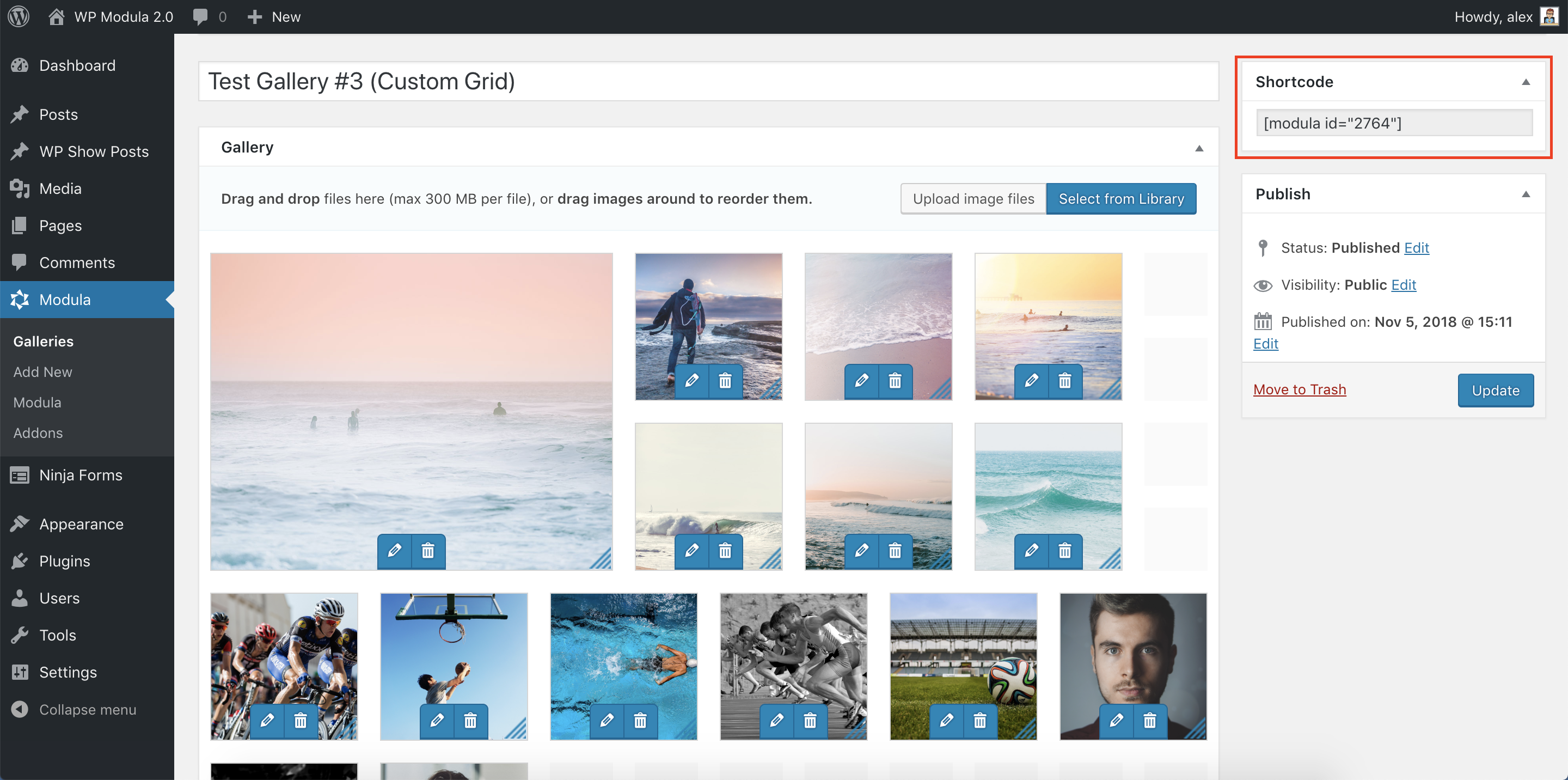
Описание основных плагинов для создания красочных галерей на сайте Wordpress
Как зафиксировать сайдбар, чтобы при прокрутке страницы блок с рекламой всегда оставался в поле
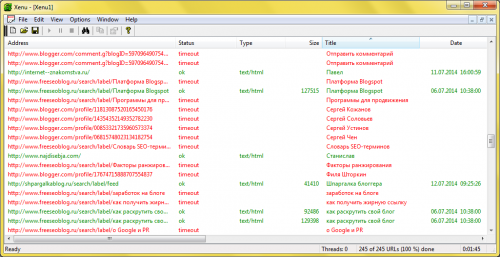
Битые ссылки - нерабочие ссылки. Которые при переходе ведут на несуществующий документ (веб старницу).
Под анонсом статьи понимается ее краткое содержание или введение. Обычно за него принимается начало записи
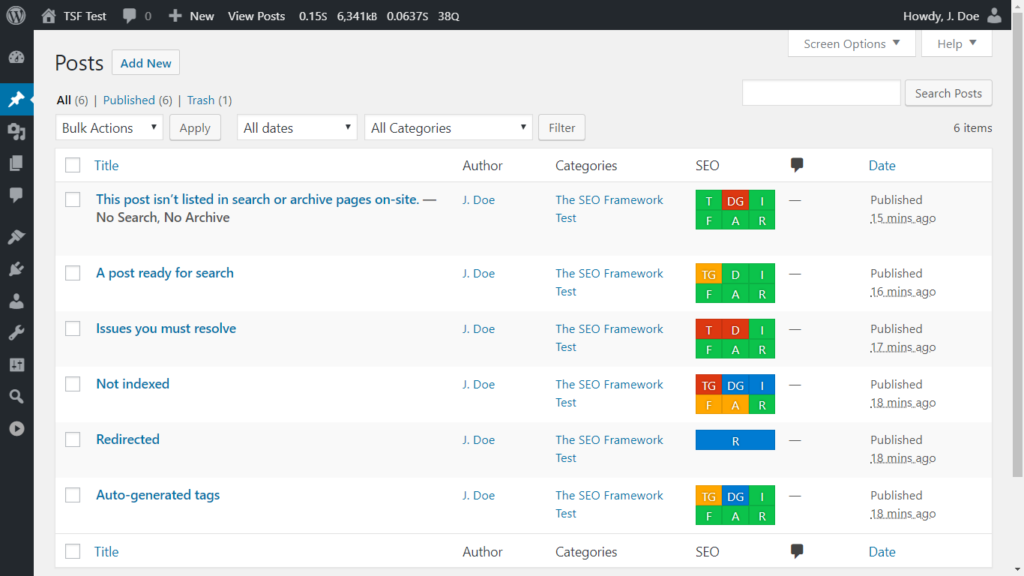
Решили продвигать сайт в поисковиках? Отлично! Но не спешите сливать бюджет на рекламу: для
Защищаем WordPress от хакерских атак. Скрываем логин, прячем вход в административную панель, оптимизируем обработку
Как заменить латиницу на кириллицу и кириллицу на латиницу. Примеры и способы: с помощью
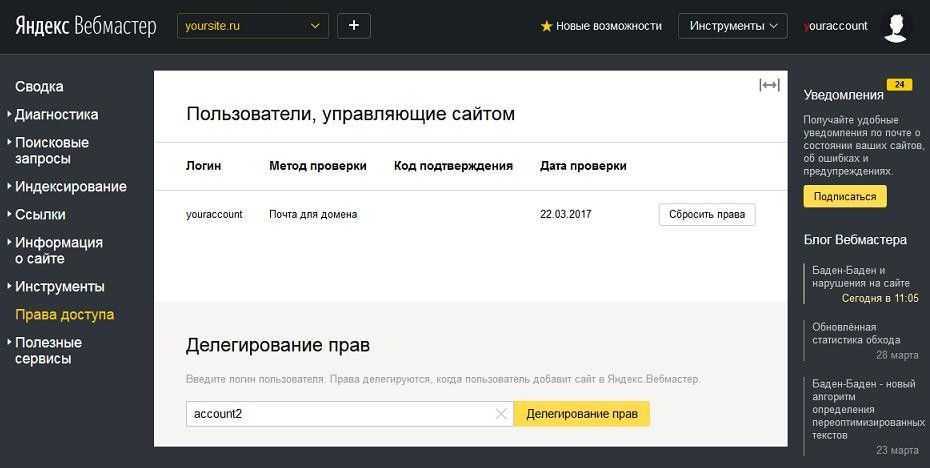
Пошаговая инструкция по добавлению сайта в Яндекс.Вебмастер: подтверждение прав, отправка карты сайта (sitemap) и
Подробная инструкция о создании и установки счетчика Liveinternet на сайт WordPress. Узнаете какие статистические